Zug, Switzerland, March 28, 2022 – The need-to-know principle controls personalized, authorized access to information – and specifically hides all other data. VNC, leading developer of open source-based enterprise applications, explains the operational implementation of these measures.
The daily flood of data has many negative consequences. However, two of them stand out as particularly disadvantageous and dangerous. Firstly, it overwhelms many people with a vast amount of unnecessary data, which has to be filtered for relevant information in a laborious and time-consuming manner. Secondly, it harbors enormous security risks, because confidential or security-relevant information is often leaked to unauthorized third parties due to a lack of targeted access control.
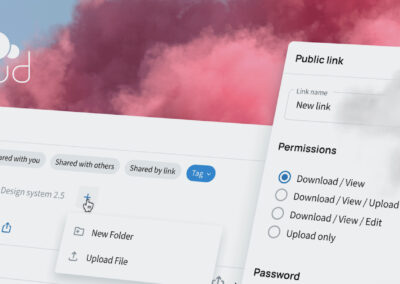
Both pitfalls can be elegantly avoided by means of the need-to-know principle. Clever authorization management ensures access only to the data and information for which the respective user profile is authorized. VNC lists the most important requirements for this:
- Compliance provides the specifications: The definition of user profiles is typically the task of the compliance department. This determines which pools of information each employee, or, if applicable, partner or supplier, has access to – and which they do not.
- Access rights in directory management: These specifications are then implemented in the directory management in the form of role-based access rights. User roles can be defined not only for specific individuals, but also for teams or departments.
- Flexible identity management: Since roles change frequently, flexible, automated identity management is a prerequisite for keeping authorizations up-to-date at all times. Without this automation, ongoing changes and innovations can no longer be managed.
- Database-level permissions: Data access rights are granted at field level, specifically to fields in relational databases. This is more difficult to regulate for object-oriented NoSQL or cloud databases, since they do not work with table functions.
- Continuous delivery concepts: In distributed environments, the authorization profiles of the various instances must be managed platform-agnostically and kept synchronized at all times. A prerequisite for this is a mirrored deployment strategy that is updated automatically.
“The need-to-know principle combines data security with the economy of knowledge. It relieves the burden on users, administrators and compliance departments alike,” explains Andrea Wörrlein, Managing Director of VNC in Berlin and member of the Board of VNC AG in Zug. “Users only get access to information that is relevant to them, allowing them to work in a more targeted and efficient manner. Compliance departments can define access authorizations to security-critical data in advance and prevent unauthorized access, and administrators find it easier to implement these specifications quickly and efficiently.”
About VNC – Virtual Network Consult AG
VNC – Virtual Network Consult AG, based in Switzerland, Germany and India, is a leading developer of open source-based enterprise applications and positions itself as an open and secure alternative to the established software giants. With VNClagoon, the organization with its global open source developer community has created an integrated product suite for enterprises, characterized by high security, state-of-the-art technology and low TCO. VNC’s customers include system integrators and telcos as well as large enterprises and institutions.
Further information on https://vnclagoon.com, on Twitter @VNCbiz and on LinkedIn.
Contact
Andrea Wörrlein
VNC – Virtual Network Consult AG
Poststrasse 24
CH-6302 Zug
Phone: +41 (41) 727 52 00
aw@vnc.biz
Beatrice Ferri
PR-COM GmbH
Sendlinger-Tor-Platz 6
80336 München
Phone: +49-89-59997-704
beatrice.ferri@pr-com.de