Even with spam filters, it can happen that dangerous emails find their way into your mailbox. Often Malware and Trojans are still sent as attachments in mails. Tech Republic has published an informative article with tips. This article summarizes some key features of counterfeit emails that help protect your PC, tablet or phone.
1) Who sent the email? First: As a sender you can manipulate many things – including using the name of well-known companies in the sender information. Be particularly vigilant if you receive an e-mail from a prominent company that you are not doing business with or whose newsletter you have not subscribed to. If you are a customer of the company, examine the exact sender address. A bank or a merchant with an own website domain will probably not send emails from an address like yahoo or gmail.
2) Does the email contain attachments? If you receive unannounced attachments in an email, caution is advised, especially ZIP files are suspicious. If in doubt, contact the company through a different route than the sender’s mail address. Nevertheless, send the file through a virus scanner, even if you are sure that the sender is genuine.
3) Does the e-mail contain legally sensitive content or threats? You can safely ignore emails from debt collection companies and alleged lawyers. Such mail is being sent exclusively by letter today. Often, such emails contain attachments with malware or Trojans. The same applies to time pressure: If you are asked to respond within an absurdly short period of time, it is probably spam or phishing.
4) Are you asked to enter data? If no other conversation has taken place be careful with your data. No legitimate customer, partner or provider will ask you for passwords, access data or personal codes without prior agreement by email.
5) What does the text look like? Spam is often characterized by errors in grammar and spelling. Bulk emails are often translated using online tools, which leads to some strange results.
You can read the complete article here.
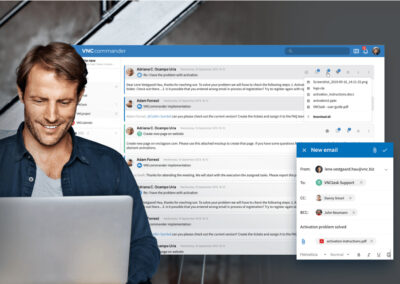
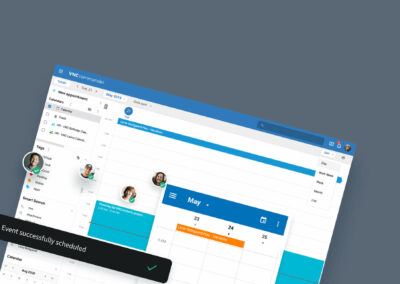
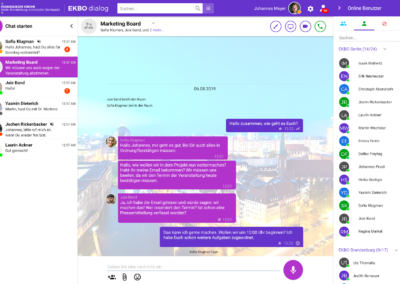
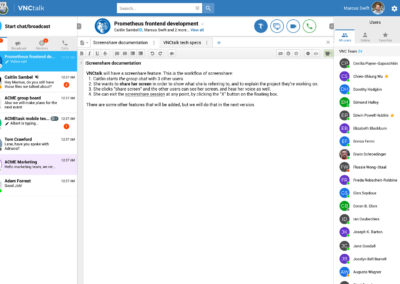
Switch to VNCmail now!
With efficient spam and virus filters, the attacks by Petya and NotPetya – two crypto-trojans that caused enormous economic damage – would probably not have been possible to the extent known.
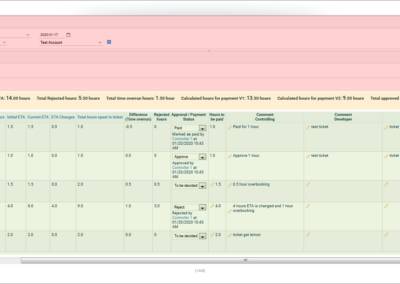
In addition to numerous innovative functions, VNCmail also offers fine-grained spam and virus filters, which do not even deliver the most dangerous emails. With various components, the spam filter can be fine-tuned to prevent unwanted emails from getting into the mailbox. The emails in question are rejected by the server immediately and therefore do not even waste space in the spam folder of the mailbox.
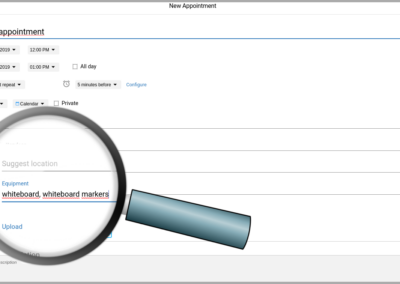
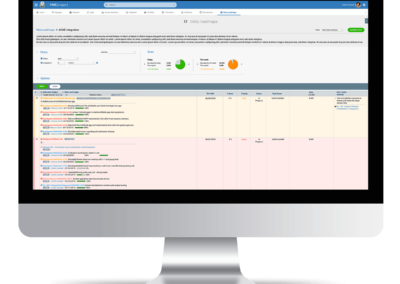
For example, a particularly accurate form of filter might look like this: ClamAV and Amavis scan incoming emails for viruses; SpamAssasin controls the content for spam and RBL (Realtime Black Lists) containing domains and IP addresses that have been used for email spam; these are immediately rejected by the server. The Sender Policy Framework SPF and OpenDKIM protect against receiving spam by allowing only controlled IP addresses and MTAs to send emails, accepting only emails from trusted senders.
Learn more about VNCmail on VNClagoon. We are also happy to answer your questions by e-mail at info@vnc.biz.